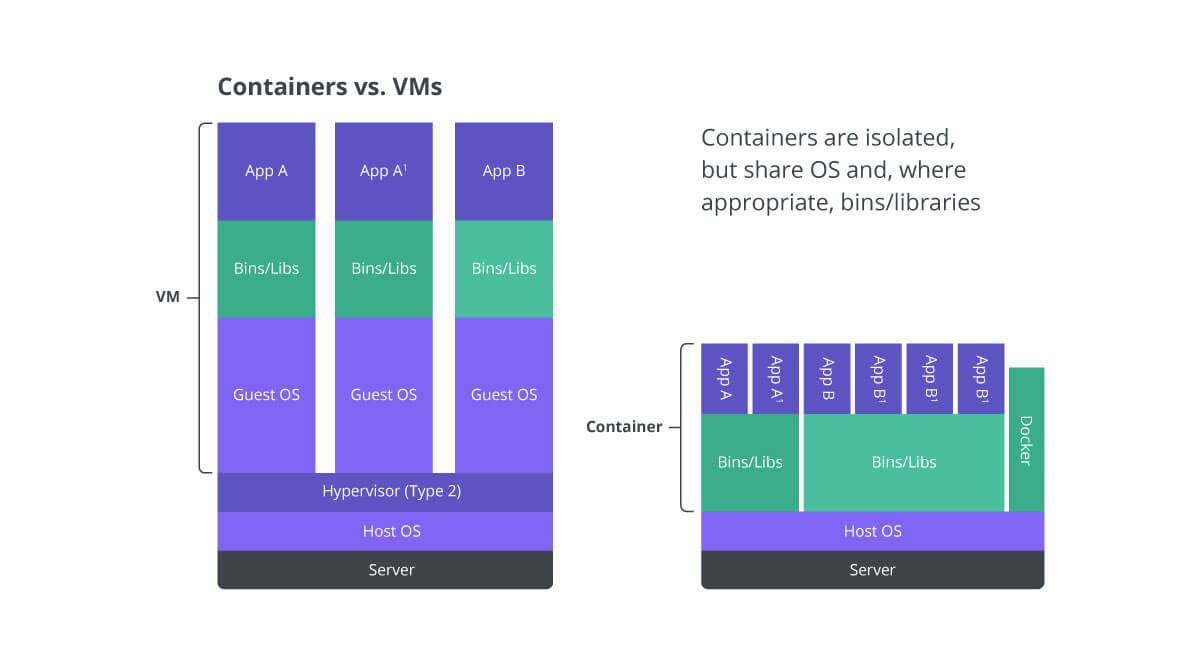
Virtual machines (VMs) have been the go-to approach for server virtualization for many years. However, with the emergence of containerization, many people wonder which approach is more secure. This article will explore the security features of containers and VMs and help you decide which is more secure.
TL;DR
Containers and virtual machines (VMs) each offer unique security features. Containers are lightweight, with a smaller attack surface and high isolation, ideal for microservices and cloud-native applications. VMs provide complete separation and hardware virtualization, making them suited for legacy applications. The choice depends on specific use cases and requirements. Interested in mastering container security? Enroll in the Certified Container Security Expert (CCSE) course today!
Security Features of Containers
Containers provide several security features that make them a popular choice in modern software development.
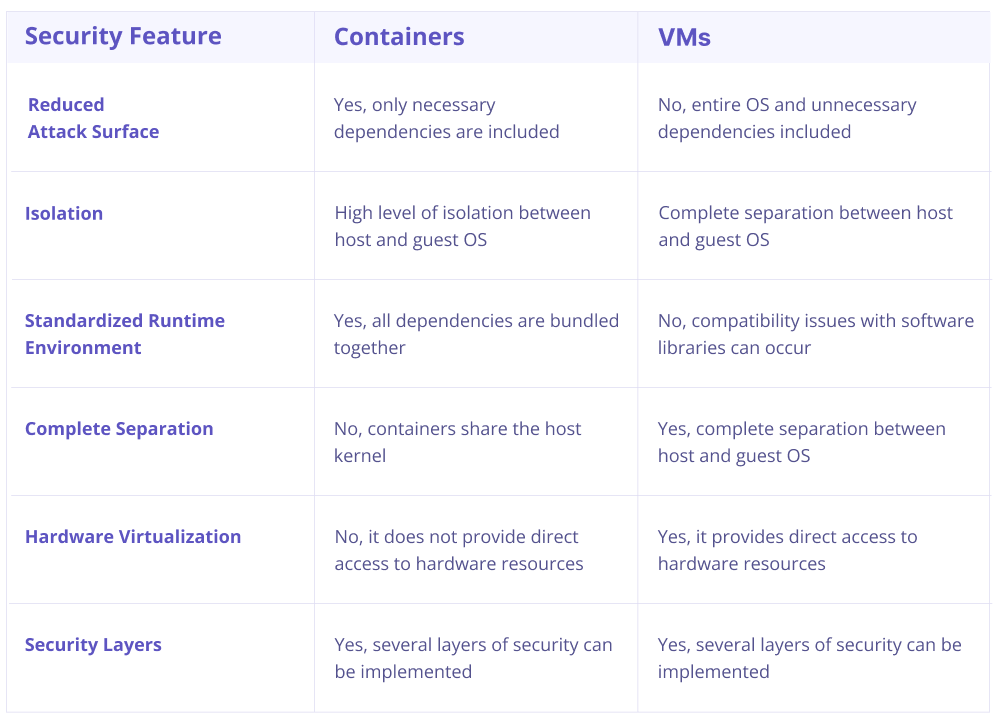
- Reduced attack surface: Containers are lightweight and only include the runtime environment and the necessary dependencies of an application. This means that the overall attack surface is much smaller than a comparable VM, reducing the potential attack points.
- Isolation: Containers provide a high level of isolation between host and guest operating systems, which helps prevent breaches and attacks from spreading.
- Immutable infrastructure: Containers are built from images, and once an image is built, it is immutable. This prevents anyone from tampering with the container, ensuring it runs in a known and trusted configuration.
- Standardized runtime environment: Containers provide a standardized runtime environment where all dependencies are bundled together, eliminating compatibility issues with software libraries. This also makes it easier to manage security updates and patches.
Security Features of VMs
VMs provide several security features that make them a popular choice in server virtualization.
- Complete separation: VMs provide complete separation of host and guest operating systems, reducing the risk of a security breach spreading or affecting other VMs or the host system.
- Hardware virtualization: VMs provide hardware virtualization, which ensures that the guest operating system has direct access to hardware resources, reducing the risk of resource conflicts.
- Security layers: VMs provide several layers of security, including host-based firewalls, virtual networks, and firmware-level protection measures.
Are Containers More Secure Than Vms?
Containers and VMs provide several security features that help protect your systems and data. However, the answer to this question depends on your specific use case and requirements. Here are some factors to consider when deciding between containers and VMs:
- Containers are lightweight and provide a smaller attack surface, making them ideal for microservices, cloud-native applications, and highly distributed systems.
- VMs provide complete separation and hardware virtualization, making them ideal for legacy monolithic applications, sensitive data, and workloads that require specific operating systems or hardware configurations.
It’s important to note that security is not a one-size-fits-all solution. The best approach is to analyze your specific use case, requirements, and budget to determine which solution is right for you.
Also Read, Container Security Best Practices
Conclusion
Containers and VMs provide unique security features that help protect your systems and data. Choosing between containers and VMs ultimately depends on your specific use case and requirements. Regardless of which solution you choose, it’s essential to implement best practices for security and regularly update and patch your systems to minimize vulnerabilities.
Interested in Container Security?




