As technology advances and businesses embrace cloud-native solutions, Kubernetes has emerged as a leading container orchestration platform. Kubernetes offers numerous features to help developers manage containerized applications effectively. One essential component for handling sensitive information, such as API keys, passwords, and certificates, is Kubernetes Secrets. However, like any other security measure, Kubernetes Secrets are not invulnerable to threats. In this article, we will explore some common security issues associated with Kubernetes Secrets and how to mitigate them.
What are Kubernetes Secrets?
Before diving into the security concerns, let’s briefly understand what Kubernetes Secrets are. In Kubernetes, Secrets are a way to store sensitive data, ensuring it is securely managed and accessed only by authorized entities. These can include database credentials, OAuth tokens, and any data that should not be exposed in plaintext within the container environment.
Kubernetes stores Secrets in an encrypted manner, providing an additional layer of protection. Users can reference Secrets in their pods, and Kubernetes automatically injects the necessary data into the containers at runtime.
Also Read, Best Kubernetes Security Books
How Secure is Kubernetes Secrets
Kubernetes Secrets are considered secure when handled with best practices. Employ encryption for data at rest, set up proper access controls using RBAC, and consider external secret management tools. Regularly rotating Secrets adds an extra layer of protection, while monitoring access helps detect any unauthorized activity. Staying up-to-date with security guidelines ensures your Secrets remain protected against evolving threats.

Kubernetes Secrets Security Issues
1. Inadequate Access Controls
One of the primary security challenges with Secrets is the misconfiguration of access controls. If not properly configured, unauthorized users or pods could gain access to sensitive information and lead to a potential data breach, compromising the entire system.
To mitigate this issue, ensure that you apply the principle of least privilege. Limit access to Secrets by using Kubernetes RBAC (Role-Based Access Control) and namespaces. Only grant access to the necessary entities and regularly review and update these permissions.
Also Read, 5 Best Kubernetes Authentication Methods
2. Storing Secrets in etcd
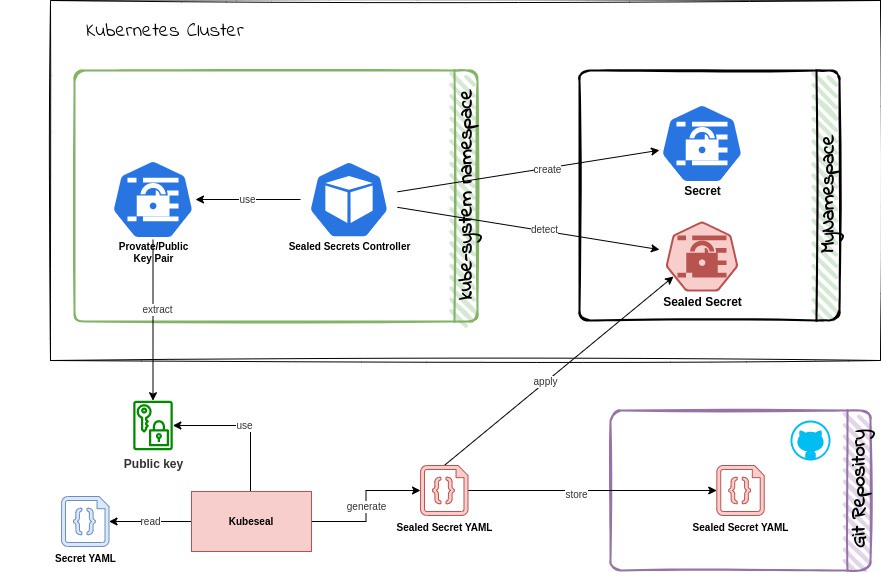
By default, Kubernetes stores Secrets in etcd, which is the cluster’s distributed key-value store. Although etcd is encrypted, it’s crucial to understand that it is not a secure storage solution designed for long-term persistence of sensitive data.
To enhance security, consider using an external Secrets management tool that is specifically designed to store and manage Secrets securely. These tools often provide additional features like rotation, auditing, and access controls.
Also Read, Kubernetes Pod Security Policies
3. Lack of Encryption in Transit
While Kubernetes encrypts Secrets at rest, there is no native encryption of Secrets in transit within the cluster. This means that if an attacker gains access to the cluster, they could potentially eavesdrop on the communication and intercept sensitive data being transferred.
To address this, always enable encryption between Kubernetes components using TLS certificates. Additionally, consider implementing network policies to restrict communication between pods, reducing the attack surface.
4. Logging and Auditing
Another security concern is the lack of proper logging and auditing for Secrets access. Without detailed logs, it becomes challenging to track who accessed Secrets and when, which makes it harder to detect suspicious activities or potential breaches.
Also Read, Best Practices for Kubernetes Security Monitoring
Also Read, Guide for Kubernetes Vulnerability Scanning
Enable auditing for Secrets access and regularly review logs for any unauthorized access attempts. By monitoring these logs, you can proactively respond to security incidents and ensure compliance with industry regulations.
Also Read, Kubernetes Security Best Practices
Also Read, Is CKS Certification Worth it
Real-World Example: Securing API Credentials
Let’s consider a real-world example of securing API credentials in a Kubernetes environment. Imagine you have a microservice-based application that requires access to various external APIs. These APIs often require authentication credentials, such as API keys or tokens.
To secure these credentials:
Create Kubernetes Secrets: Use ‘kubectl create secret’ to create Secrets to store API credentials
Apply RBAC: Implement RBAC rules to grant access to the Secrets only to the specific microservices that require them. Avoid giving full access to all resources.
Use Environment Variables: Inject the Secrets into the microservice pods as environment variables rather than directly mounting them as files. This reduces the risk of exposing the Secrets unintentionally.
Rotate Secrets Regularly: Rotate the API credentials periodically, and update the corresponding Kubernetes Secrets accordingly. Automation tools can help in managing this process.
Also Read, Best Certifications to Become a Kubernetes Security Expert
Also Read, Scope for Kubernetes Security Engineers
Conclusion
Kubernetes Secrets is a vital component for securely managing sensitive information within a Kubernetes cluster. However, like any security measure, they require careful configuration and management. By addressing the mentioned security issues and following best practices, you can significantly enhance the security of your Kubernetes Secrets and protect your containerized applications from potential breaches.
Also Read, Best Steps for Automating Security in Kubernetes Pipelines
How to Get Kubernetes Security Training?
You can get trained in Kubernetes security by enrolling in our Cloud-Native Security Expert (CCNSE) course, which provides hands-on training in important concepts such as:
Hacking Kubernetes Cluster, Kubernetes Authentication and Authorization, Kubernetes Admission Controllers, Kubernetes Data Security, Kubernetes Network Security, Defending Kubernetes Cluster
Course Highlights:
- 50 + guided exercises uniquely designed by industry experts
- 24/7 instructor support
- Browser-based labs for hands-on training
- Lifetime access to course manuals and videos




